Securing Email Attachments—Your Biggest Vulnerability, Solved
Email remains the top attack vector for malware delivery. Here's how to close that gap.
Every day, organizations receive thousands of files—email attachments, documents from partners, downloads from the web. And every day, cybercriminals exploit this trust with attacks that slip past traditional security defenses.
If your organization relies on antivirus software and sandboxing to protect against malicious files, you may be more vulnerable than you think. Here's why these legacy approaches are struggling to keep up.
Traditional antivirus works by comparing files against a database of known threats. When a file matches a signature, it gets blocked. The problem? Attackers create new, unique malware variants faster than security vendors can catalog them. According to the AV-TEST Institute, over 450,000 new malware samples are registered every single day.
This means your antivirus is always playing catch-up, protecting you only against threats that have already been discovered—and only after your vendor has created a signature for them.
Zero-day attacks, by definition, have no existing signature. They pass through antivirus scanners undetected.
Sandboxing emerged as a solution to the signature problem. Instead of matching files against known threats, sandboxes execute files in an isolated environment and observe their behavior. If the file does something malicious, it gets flagged.
In theory, this catches zero-day threats. In practice, attackers have adapted.
Modern malware is often "sandbox-aware." It detects when it's running in a virtual environment and simply behaves normally—waiting to execute its payload until it reaches a real endpoint. Other evasion techniques include time-delayed execution, user interaction requirements, and environment fingerprinting.
A study by Lastline found that over 75% of malware samples exhibited some form of sandbox evasion behavior. Your sandbox may be giving files a clean bill of health when they're anything but.
Even when sandboxing works, it introduces delays. Files must be executed, monitored, and analyzed—a process that can take minutes or even longer. In high-volume environments like email gateways, this creates bottlenecks that impact productivity.
IT teams often face pressure to reduce analysis time, which means lowering security thresholds. The result is a weakened security posture in the name of operational efficiency.
The fundamental flaw in both antivirus and sandboxing is their reliance on detection. They try to determine whether a file is malicious—a question that's becoming increasingly difficult to answer accurately.
What if, instead of trying to detect threats, we simply removed the possibility of threats altogether?
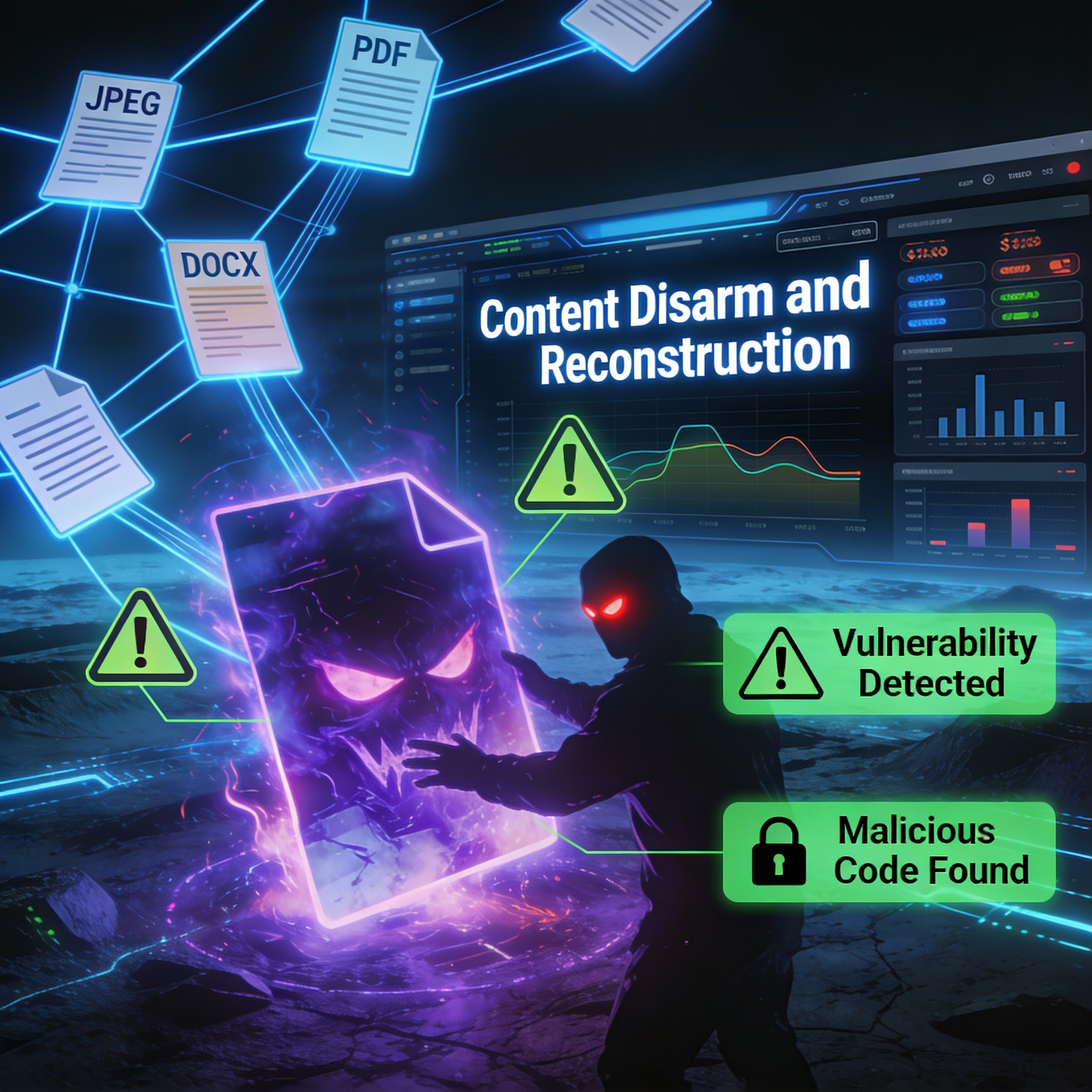
This is the principle behind Content Disarm and Reconstruction (CDR) technology. Rather than scanning files for known or suspected malware, CDR assumes every file could be dangerous and reconstructs it from scratch, preserving only the safe, usable content.
No signatures to update. No behavioral analysis to evade. No detection to bypass.
In our next post, we'll explore how CDR works and why organizations across industries are adopting it as their primary defense against file-based threats.

Email remains the top attack vector for malware delivery. Here's how to close that gap.
A critical Windows imaging vulnerability demonstrates how attackers weaponize everyday files and why Content Disarm and Reconstruction technology...

Stop trying to detect threats. Eliminate them before they have a chance to execute.