CVE-2025-50165 exposes why detection-based security fails against file-borne threats
A critical Windows imaging vulnerability demonstrates how attackers weaponize everyday files and why Content Disarm and Reconstruction technology...
2 min read
Klearis 30/11/25 00:24
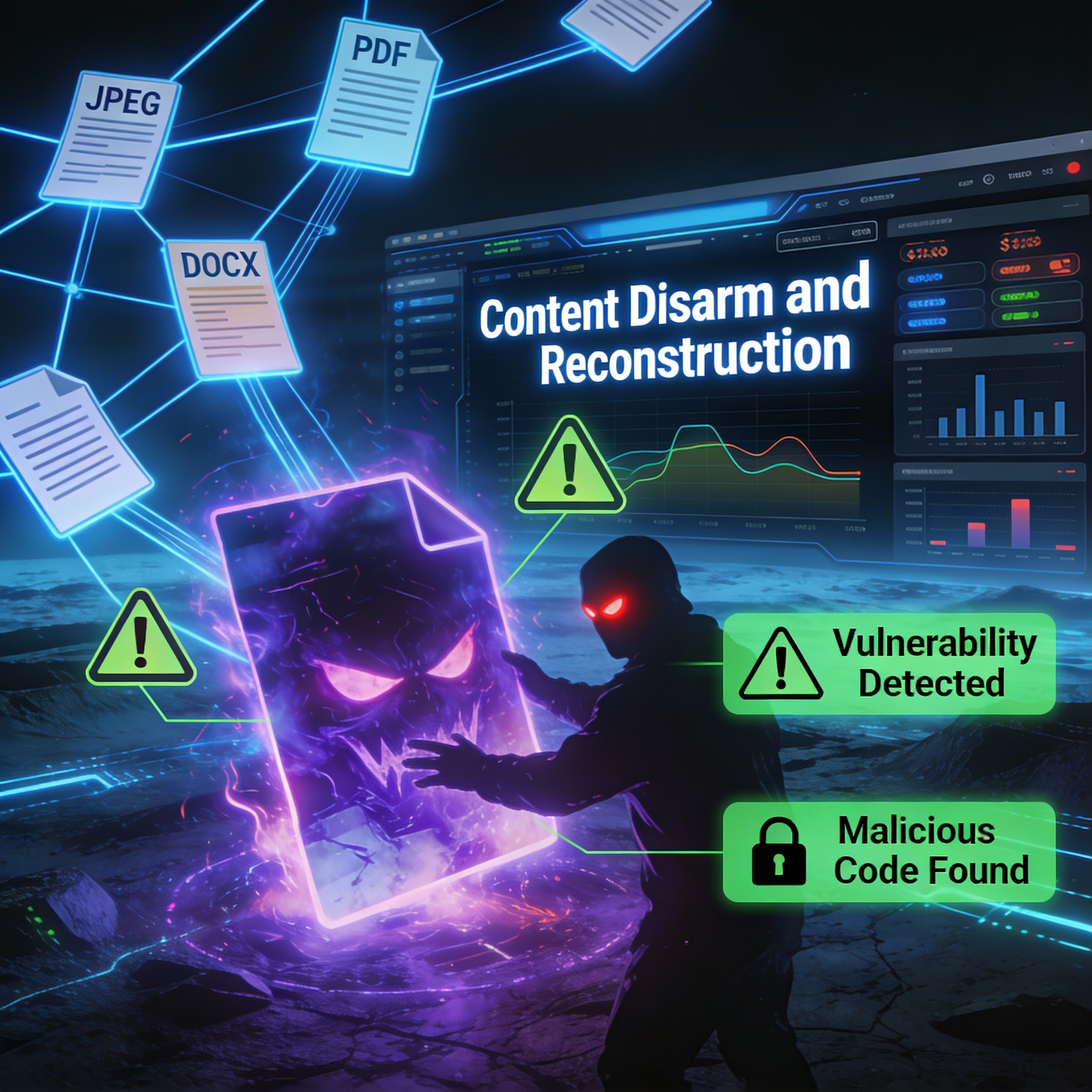
In our previous post, we explored why traditional security tools—antivirus and sandboxing—are struggling against modern file-based attacks. Today, we'll introduce a fundamentally different approach: Content Disarm and Reconstruction, or CDR.
CDR is a file sanitization technology that takes a prevention-first approach to security. Instead of trying to determine whether a file is malicious, CDR treats every file as potentially dangerous and processes it accordingly.
Here's how it works:
The CDR engine deconstructs incoming files, analyzes their structure, extracts only the legitimate business content, and rebuilds clean files from scratch. Any potentially malicious elements—hidden scripts, embedded macros, exploit code—are left behind in the process.
The result is a sanitized file that looks and functions exactly like the original but contains none of the potential threats.
When a file enters a CDR system, several things happen:
Analysis: The system identifies the true file type (regardless of extension) and validates its structure against known-good specifications for that format.
Deconstruction: The file is broken down into its component elements—text, images, formatting, metadata, and so on.
Threat Removal: Active content that could harbor threats—macros, JavaScript, embedded objects, OLE links—is identified and neutralized or removed entirely.
Reconstruction: A new, clean file is built using only the verified safe elements. This new file conforms to the file format specification and functions normally for business use.
The entire process happens in milliseconds, with no noticeable delay for end users.
Traditional security asks: "Is this file malicious?" CDR asks a different question: "What in this file is definitely safe?"
This shift in philosophy has profound implications:
Zero-day immunity: Because CDR doesn't rely on signatures or behavioral analysis, it neutralizes threats that have never been seen before. The attack technique doesn't matter—if it's hidden in file structures, it gets removed.
No evasion possible: Sandbox-aware malware can hide from behavioral analysis. But it can't hide from a process that strips away everything except known-safe content. There's nothing to evade.
Speed at scale: CDR processing takes milliseconds, not minutes. This makes it practical for high-volume environments like email gateways where sandboxing creates unacceptable delays.
Consistent protection: Every file is processed the same way. There's no risk of a sophisticated threat slipping through because it didn't trigger detection thresholds.
A common concern with file sanitization is whether it affects document usability. With Klearis CDR, the answer is no—at least not in ways that impact legitimate business use.
Klearis CDR preserves all the content users need: text, formatting, images, tables, charts. What gets removed are high-risk elements like macros and scripts—elements that most business documents don't require and that represent significant attack vectors when they're present.
For organizations that do require macro-enabled documents, policies can be configured to allow trusted sources or to provide the original file after additional verification steps.
CDR technology is gaining recognition across the security industry. Gartner has identified CDR as a key technology for protecting against advanced file-based threats. Organizations in finance, healthcare, government, and critical infrastructure are adopting CDR to protect their most sensitive environments.
Klearis CDR is designed for enterprise email security, web gateway protection, and file upload sanitization—providing comprehensive protection wherever files enter your organization.
In our next post, we'll focus on one of the most critical use cases: protecting email attachments, the number one vector for file-based attacks.
A critical Windows imaging vulnerability demonstrates how attackers weaponize everyday files and why Content Disarm and Reconstruction technology...

Antivirus and sandboxing were built for yesterday's threats. Today's attackers have moved on. Every day, organizations receive thousands of...

Email remains the top attack vector for malware delivery. Here's how to close that gap.