Why Traditional Security Can't Stop Modern File-Based Attacks?
Antivirus and sandboxing were built for yesterday's threats. Today's attackers have moved on. Every day, organizations receive thousands of...
Despite decades of investment in email security, malicious attachments remain one of the most effective ways for attackers to breach organizations. According to Verizon's Data Breach Investigations Report, email continues to be the primary delivery mechanism for malware, with attachments playing a central role in successful attacks.
Why does this problem persist? And what can organizations do to finally solve it?
Your employees receive dozens—perhaps hundreds—of emails with attachments every day. Invoices, contracts, reports, spreadsheets. These files are essential to business operations, which means blocking all attachments isn't an option.
Traditional email security relies on a combination of approaches:
Each of these has value, but none is sufficient on its own—or even in combination.
Spam filters can be bypassed through compromised legitimate accounts. Antivirus misses zero-day threats. Sandboxing can be evaded by sophisticated malware. And even well-trained employees make mistakes, especially when attackers use convincing pretexts and time-pressured scenarios.
The result? Malicious attachments continue to reach inboxes, and eventually, someone clicks.
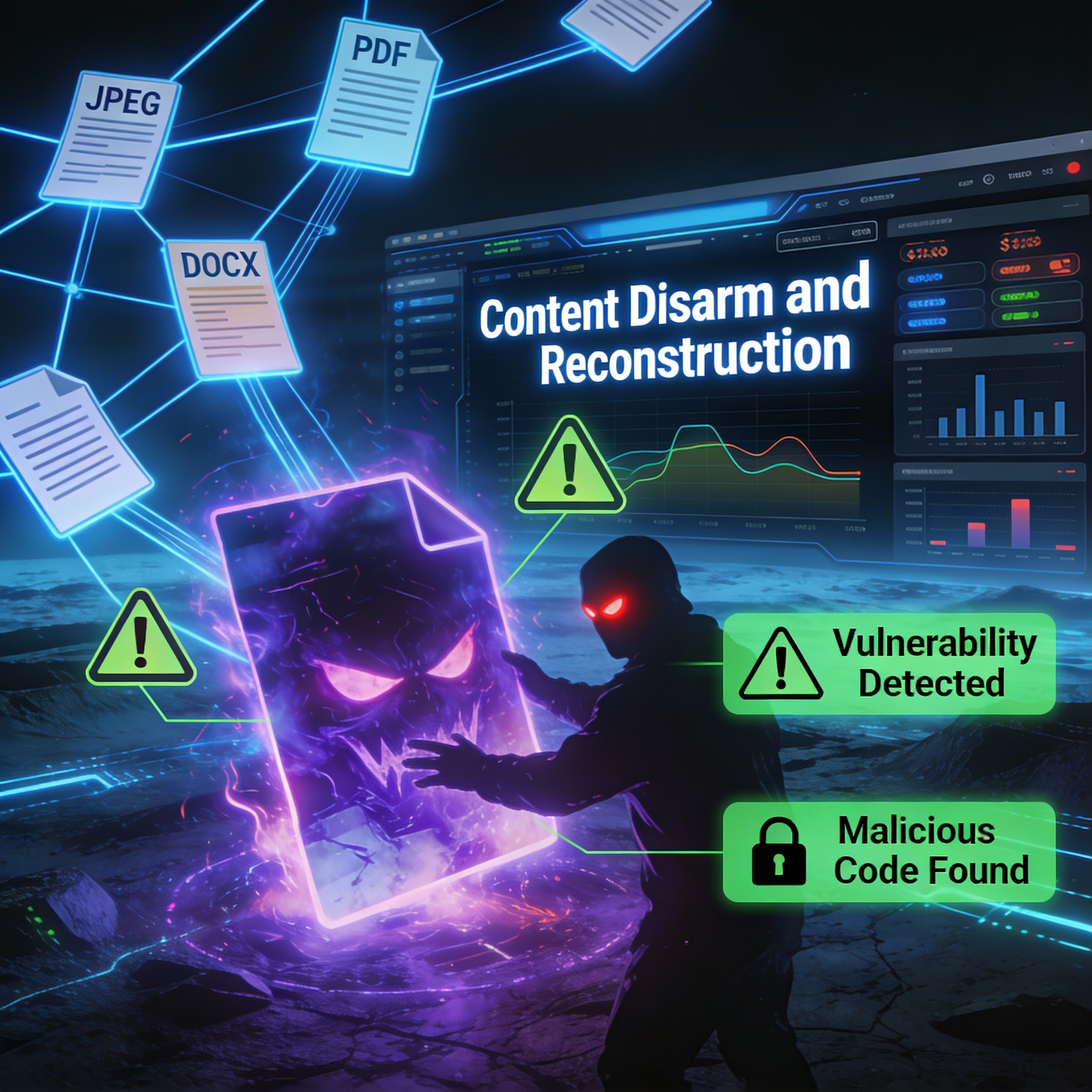
Content Disarm and Reconstruction (CDR) offers a different model for email attachment security. Rather than trying to detect which attachments are dangerous, CDR assumes all attachments could be dangerous and sanitizes them accordingly.
When an email with attachments passes through a CDR-enabled gateway:
The entire process happens in real-time, with no perceptible delay. Users receive their files and continue working normally—but any hidden threats have been neutralized before delivery.
One of the practical advantages of Klearis CDR is that it integrates seamlessly with existing email infrastructure:
On-premises mail servers: Integration via SMTP relay or mail transfer agent (MTA) configurations allows organizations to sanitize attachments before they reach internal mail servers.
Microsoft 365: For organizations using cloud email, Klearis can process attachments through connector configurations, ensuring files are sanitized before reaching user mailboxes.
Secure email gateways: CDR complements existing email security solutions, adding a layer of file sanitization that addresses the gaps in detection-based approaches.
This means organizations don't need to replace their existing security investments. Klearis CDR adds a critical layer of protection that works alongside antivirus, anti-spam, and other email security tools.
Consider the practical difference CDR makes:
Without CDR: An employee receives an Excel file that appears to be an invoice from a known supplier. Antivirus scans it and finds nothing suspicious—the malware uses a new technique with no existing signature. The sandbox analysis times out before the time-delayed payload activates. The employee opens the file, a macro executes, and the organization is compromised.
With Klearis CDR: The same Excel file arrives. The CDR engine processes it, strips out the macro code, and delivers a clean spreadsheet with all the invoice data intact. The employee opens the file and continues their work. The attack fails silently—no alert, no incident, no breach.
This is the power of prevention over detection. The threat is neutralized before any analysis is required, before any user decision is needed.
Email will remain a critical attack vector because it's central to how organizations communicate. The question isn't whether attackers will target your email—it's whether your defenses are adequate when they do.
If your current approach relies on detecting malicious attachments, you're accepting a level of risk that CDR can eliminate. Every file that bypasses your detection is a potential breach. Every zero-day that evades your sandbox is an open door.
Klearis CDR provides the prevention-first protection that modern email security requires. Attachments are sanitized in real-time, threats are neutralized before delivery, and your users can work confidently knowing their files are safe.

Antivirus and sandboxing were built for yesterday's threats. Today's attackers have moved on. Every day, organizations receive thousands of...

Stop trying to detect threats. Eliminate them before they have a chance to execute.
A critical Windows imaging vulnerability demonstrates how attackers weaponize everyday files and why Content Disarm and Reconstruction technology...